a pen-tested, secure part of your pipeline
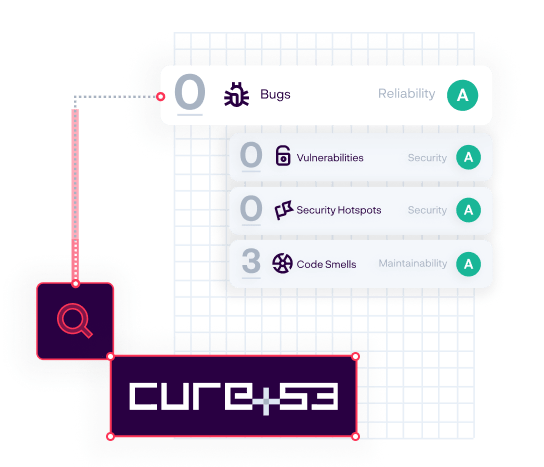
A routine part of delivery is periodic penetration testing. In addition to hardening SonarQube itself, we’ve also hardened our own build pipeline so you can be sure we’re delivering SonarQube to you securely. You can read more about what our penetration test, Cure53, had to say about SonarQube 9.8 and 9.9 LTS.