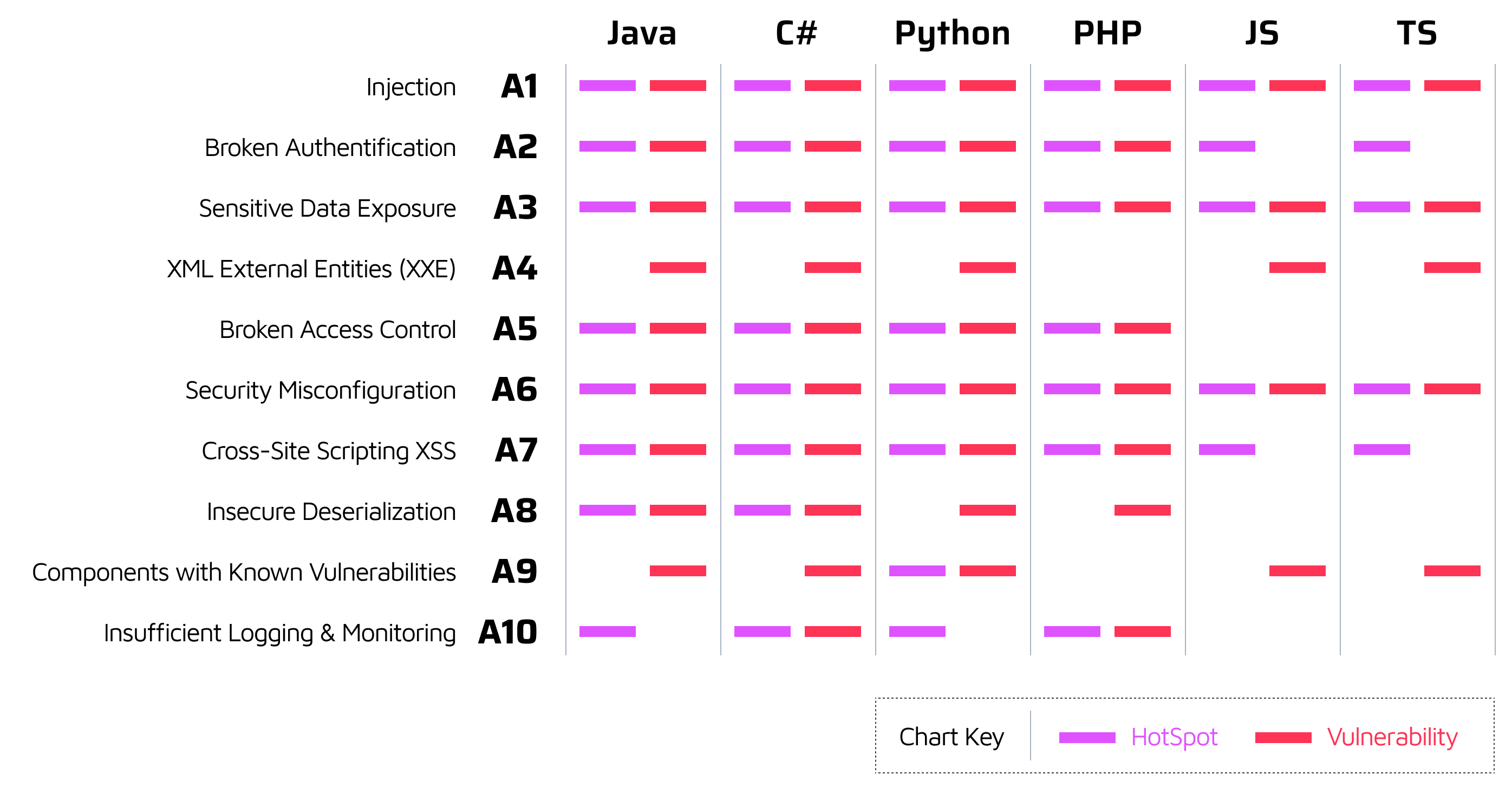
OWASP/CWE Top 25 Security Reports in Projects and Portfolios
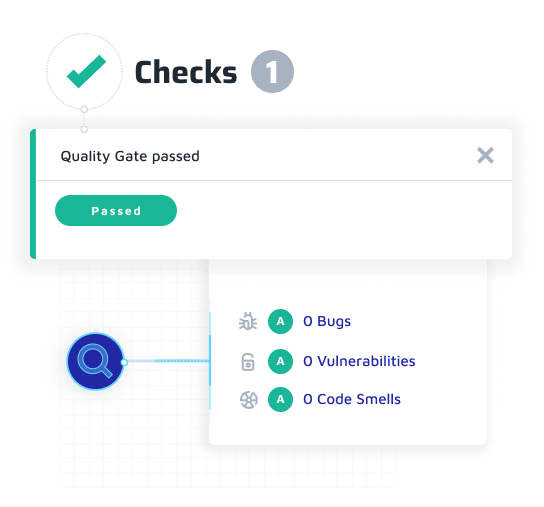
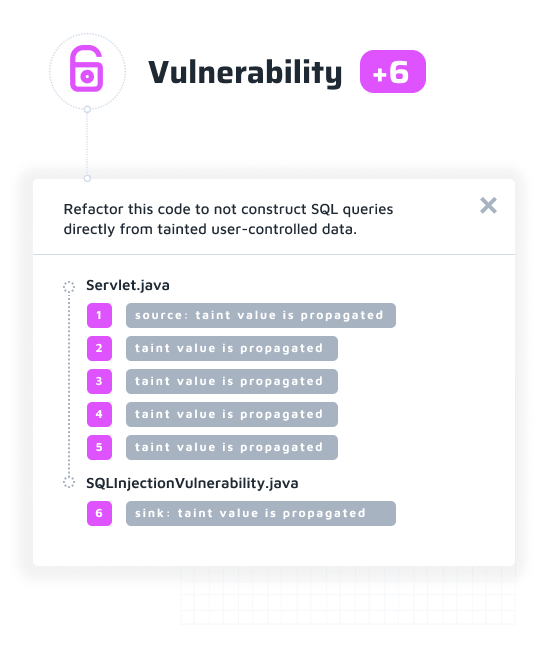
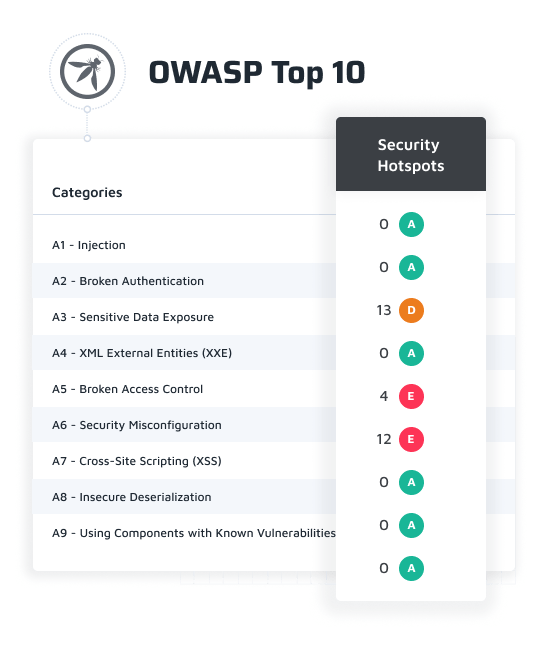
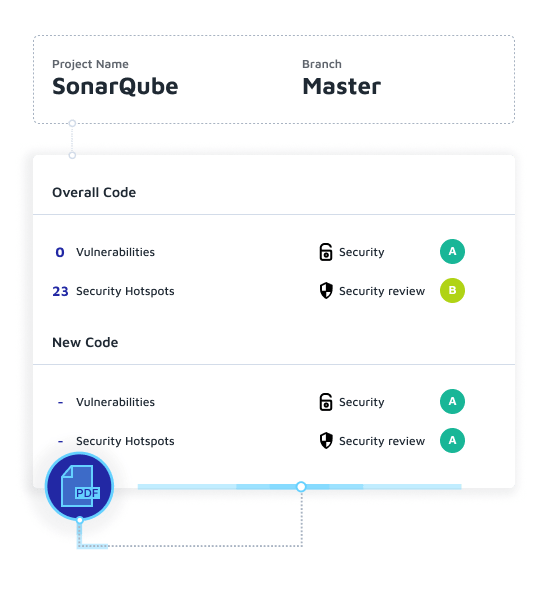
- Dedicated reports to track application security against categories of the OWASP and CWE Top 25 standards
- Shortens the Security Vulnerability feedback loop and helps developers fix security holes faster
- Export a PDF of the top reports